Managed service providers operate in an environment where a single patching decision can ripple across dozens of client environments simultaneously. Unlike an internal IT team managing one organization’s fleet, an MSP must maintain consistent standards while accommodating meaningful differences between clients: different operating systems, different risk tolerances, different compliance obligations, and different windows of availability for maintenance activity. A one-size-fits-all approach to update deployment is not just inefficient in this context; it is a liability.
The answer is neither fewer updates nor more manual oversight. It is a more sophisticated policy architecture. Multi-tenant patch management software for MSPs makes it possible to define and enforce update rings, build version approval workflows, and apply different policies to different client organizations from a single centralized console, without sacrificing per-client granularity.
What Update Rings Are and Why They Matter
An update ring is a defined group of devices that receives a software update at a specific stage and time in a staged deployment sequence. Rather than pushing an update to all endpoints simultaneously, an MSP divides the rollout into rings: an early group that receives updates first and serves as a validation layer, followed by progressively larger groups as confidence in the update grows.
The purpose is risk distribution. If an update causes an unexpected interaction with a specific application, hardware configuration, or operating system version, that problem surfaces in the early ring, typically composed of low-risk, representative machines rather than across the entire client fleet. By the time the update reaches the broader population of production devices, it has been validated against a meaningful sample.
For MSPs, this concept becomes more complex because each client may require its own ring structure. A healthcare client with regulated systems and tight uptime requirements will have different ring definitions than a professional services firm with a more flexible tolerance for update-related disruptions. Managing these configurations manually across dozens of client environments is not sustainable. A multi-tenant platform allows the MSP to define a ring architecture once at the template level, then adapt and apply it per client without having to start from scratch for each.
Version Approval as a Formal Control
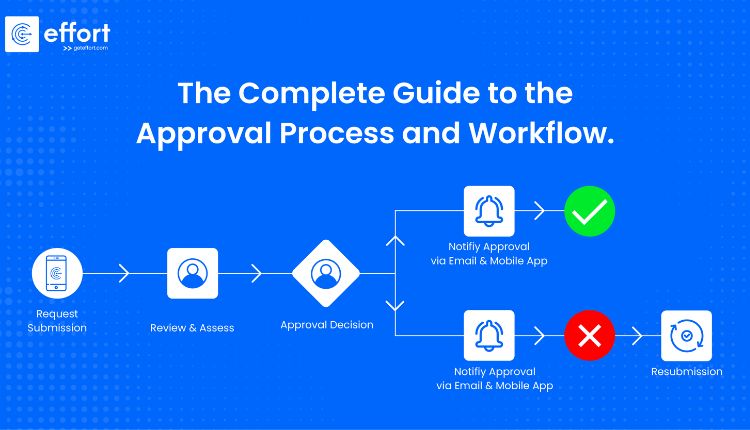
Not every update should be deployed as soon as it is available. Version approval workflows introduce a structured review step between the availability of an update and its entry into the deployment queue. This is particularly important for major operating system updates, application upgrades that change functionality, and any software update tightly integrated with client-specific workflows.
The approval process typically involves several questions. Has this version been tested against the software stack this client uses? Are there known issues reported by other organizations running the same update in similar environments? Does the client have any active projects or operational constraints that would make this a poor time to introduce a change? Is there a rollback path if the update needs to be reversed?
As noted in this overview, automated tools can handle the deployment mechanics and post-patching verification once a decision has been made, but the policy framework governing which updates proceed and when remains a human responsibility rooted in documented process. Version approval workflows formalize that responsibility, creating a record of who approved what and when, which is valuable both operationally and for compliance purposes.
In a multi-tenant environment, approval workflows may be configured at the MSP level, delegated to a client-side stakeholder for specific categories of updates, or held entirely by the MSP depending on the service agreement. The key is that the process is defined and enforced by the platform rather than communicated via email threads and tracked in spreadsheets.
Building Policy Templates That Scale Across Clients
The operational efficiency of a well-structured multi-tenant patching platform depends heavily on the quality of its policy templates. A template is a reusable policy configuration that defines ring structure, deployment windows, approval requirements, reboot behavior, and exception handling. When a new client environment is onboarded, the MSP applies the appropriate template and adjusts only the parameters that genuinely differ for that client.
This approach reduces onboarding time, ensures baseline consistency, and makes policy audits tractable. If a template needs to be updated because a compliance requirement has changed, because a new class of vulnerability has prompted a revision of critical patching timelines, or because operational experience has revealed a flaw in the original design, the change can be propagated to all environments using that template simultaneously rather than requiring manual updates across each client instance.
Well-designed templates also account for emergency scenarios. A standard deployment window might specify off-hours deployment across a 48-hour ring progression. An emergency patch template bypasses the extended testing ring and compresses the deployment window to hours rather than days, with appropriate approvals required to invoke it. Having this defined in advance means that when a critical zero-day vulnerability is disclosed, the MSP has a documented, repeatable emergency response path rather than an improvised one.
Multi-Tenancy as an Organizational Requirement, Not a Feature
Multi-tenancy in patch management is sometimes described as a convenience, the ability to see all clients from one interface. This understates its importance. For an MSP, multi-tenancy is the architectural foundation that enables policy-driven patching at scale.
Without a true multi-tenant architecture, an MSP has two bad choices: a single shared policy that applies uniformly to all clients regardless of their individual needs, or separate tool instances for each client that must be maintained, configured, and monitored independently. The first choice creates compliance and operational risk. The second creates administrative overhead that scales linearly with client count, making consistent enforcement nearly impossible.
A multi-tenant platform with per-client policy isolation allows the MSP to operate more like an internal IT team for each client, with knowledge of that client’s specific environment, tailored configurations, and per-client reporting while still operating at MSP scale from a centralized management layer. This is the architecture that makes service delivery both personal and scalable.
NIST SP 800-128, this guide for security-focused confilifecycle, aguration management, outlines that effective configuration control requires defined processes for managing changes throughout the system lifecycle, a principle that applies directly to how MSPs should structure their patching and version approval workflows across client environments.
Exceptions, Overrides, and Compliance Documentation
No patching policy operates without exceptions. A device may be excluded from a deployment ring temporarily because it is undergoing migration. A client may request a version hold because a business-critical application has not yet been certified for a new release. An emergency override may be needed to deploy a patch outside the standard window in response to an active threat.
The discipline of exception management is where many MSPs run into difficulty. Exceptions that are verbally agreed to, informally tracked, or simply allowed to lapse without review accumulate into a hidden backlog of known-but-unpatched systems. From a compliance standpoint, an exception without documentation is indistinguishable from a failure.
Platform-enforced exception workflows require that exceptions be formally created, assigned a duration, approved by the appropriate stakeholder, and reviewed before they are extended. The audit trail this creates serves two purposes: it allows the MSP to demonstrate to clients and auditors that deviations were intentional and managed rather than accidental, and it creates a forcing function for reviewing whether the exception is still warranted.
Frequently Asked Questions
What is an update ring, and how should an MSP define one for a client?
An update ring is a group of devices that receives software updates at various stages in a rollout. MSPs should start by selecting a small, representative group of lower-risk devices for initial updates, serving as a validation group. If successful, the updates are forwarded to a larger group and eventually to all relevant devices. Ring definitions should consider device criticality, operational role, and the client’s disruption tolerance. Multi-tenant patch management platforms typically allow custom ring definitions per client.
How does a version approval workflow differ from simply delaying a deployment?
A deployment delay lacks documentation, ownership, and review triggers. In contrast, a version approval workflow is a formal process that requires authority approval before deployment, based on documented criteria, and generates a record for accountability. For MSPs, this workflow can also mandate client sign-off on certain updates to address client concerns.
How should an MSP handle patching exceptions to remain compliant?
Exceptions should follow a documented workflow detailing the reason, affected systems, duration, approver, and any compensating controls. The workflow must require an active decision to extend or close the exception, preventing indefinite delays. Open exceptions pose a compliance risk, so a managed patch platform can enhance tracking and reduce the risk of overlooked exceptions.