We live in an era where artificial intelligence can write software, surgeons can operate on patients from across the globe via robotics, and massive financial trades are executed in milliseconds. Yet, if you ask a hospital administrator to send you a copy of your complete medical history, they will almost certainly refuse to send it to your standard email address.
For the average consumer, this feels like an infuriating bureaucratic bottleneck. Why does the medical, legal, and financial world still rely on strict, point-to-point transmission protocols instead of the sheer convenience of a standard email attachment?
The answer is not a stubborn refusal to adopt new technology. The answer is that standard email is a fundamental cybersecurity nightmare. To understand why heavily regulated industries must bypass the traditional inbox, we have to look at how data travels, where it rests, and why “Zero Retention” architecture has become the gold standard for institutional security.
The “Store-and-Forward” Liability
The core flaw of standard email lies in its architecture. Email uses a “store-and-forward” model. When you hit send on a PDF of a legal contract or a patient’s MRI results, that file does not travel directly from your computer to the recipient’s computer.
Instead, the email hops from your local network to an outbound server, then potentially bounces across several intermediate, third-party routing servers across the internet, before finally resting on the recipient’s inbound mail server.
Every single time that email stops at a server, a copy of that data is temporarily (or sometimes permanently) stored. Furthermore, once it reaches its destination, it sits idle in an inbox. Hackers rarely intercept data while it is moving at the speed of light through a fiber optic cable; they target idle data resting on a server. An inbox full of unencrypted PDFs is a treasure trove for ransomware gangs.
The Cryptographic Tunnel
Regulated industries recognized decades ago that the only legally compliant way to send data is via direct, point-to-point transmission. While the old analog copper wires provided this direct connection, they lacked modern digital encryption.
The modern solution involves bridging the strict point-to-point philosophy of the past with the advanced cryptography of the present. This is achieved by utilizing an encrypted online fax service. Rather than acting as a traditional email server that holds onto your data indefinitely, these enterprise-grade platforms act as highly secure, ephemeral transit hubs.
When a document is uploaded for transmission, it doesn’t bounce across the open internet. It is pulled through a secure cryptographic tunnel utilizing Transport Layer Security (TLS 1.2 or higher). This tunnel ensures that even if a “Man-in-the-Middle” attacker intercepts the data stream, all they will see is scrambled, mathematically impenetrable static.
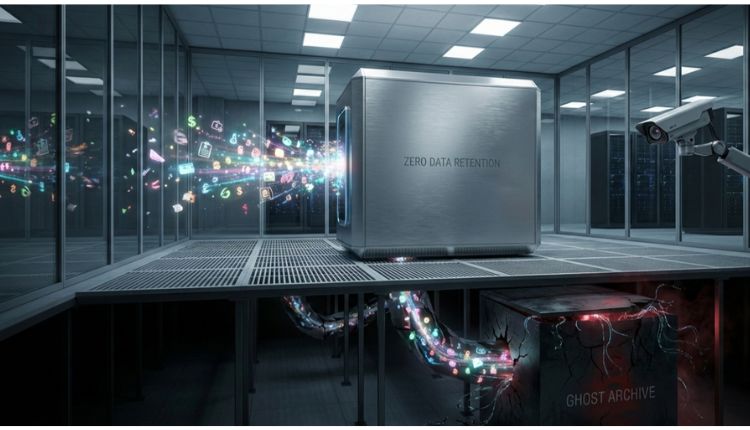
The Brilliance of Zero Retention
However, encrypting the data while it is moving is only half the battle. The true genius of a highly compliant transmission system is what it does with the document after it arrives.
To comply with the strictest regulations—such as HIPAA in healthcare, FERPA in education, or PCI-DSS in finance—a transmission server must employ “Zero Retention” architecture.
When a sensitive document enters the secure data center, it is immediately armored with Advanced Encryption Standard (AES) 256-bit encryption. The server processes the file, dials the recipient’s secure digital endpoint (or legacy machine), and delivers the payload.
The millisecond the receiving endpoint confirms a successful delivery, the zero-retention protocol triggers. The transmission server instantly and permanently shreds the encrypted document from its own hard drives. There is no outbox. There is no sent folder full of sensitive patient records sitting on a third-party server waiting to be compromised. The data is simply gone.
The Indestructible Audit Trail
If the document is completely destroyed, how does a hospital or law firm legally prove they sent it?
While the payload (the document itself) is purged, the metadata surrounding the event is permanently preserved. The secure server generates a cryptographic audit trail that logs the exact date, the precise millisecond of transmission, the sender’s authenticated IP address, the recipient’s routing number, and the cryptographic success code.
This ledger provides undeniable, court-admissible proof of delivery without ever exposing the sensitive information contained within the actual file.
Conclusion
The refusal of healthcare providers and financial institutions to rely on standard email is not a technological failure; it is a calculated, highly engineered defense mechanism. By combining military-grade encryption with the ruthless efficiency of zero-retention architecture, modern digital transmission ensures that your most sensitive, private information never sits idle long enough to become a target.